41 aws security best practices
AWS Security Best Practices Checklist - DZone Security Assign individual IAM users with necessary permissions to enable login. Ensure User Accounts also have MFA authentication. IAM Access Keys must be rotated at periodic intervals. Ensure a strong... Learn best practices for securing your AWS account and resources Here are some best practices to consider when securing your account and its resources: Safeguard your passwords and access keys Activate multi-factor authentication (MFA) on the AWS account root user and any users with interactive access to AWS Identity and Access Management (IAM) Limit AWS account root user access to your resources
13 AWS Security Best Practices - Check Point Software By following this AWS security best practices checklist, it is possible to improve the security of an AWS deployment. Identify Security Requirements 1. Define and Categorize Assets in AWS: It is impossible to secure systems that you don't know exist.
Aws security best practices
AWS Foundational Security Best Practices standard The AWS Foundational Security Best Practices standard is a set of controls that detect when your deployed accounts and resources deviate from security best practices. The standard allows you to continuously evaluate all of your AWS accounts and workloads to quickly identify areas of deviation from best practices. AWS Security Best Practices | Cyphere - thecyphere.com Using security best practices helps businesses establish a security baseline and protect their AWS infrastructure from potential risks. By implementing these practices, companies can reduce the likelihood of data breaches, leaks, and other threats. Additionally, using security best practices can help businesses detect and respond to threats ... 10 AWS Security Best Practices For Developers | YourTechDiet Here are the 10 AWS Security Best Practices for Developers. Enable AWS CloudTrail; AWS CloudTrail is a tool that allows you to record API logs for security analysis, compliance auditing, and change tracking. With it, one can create trails of breadcrumbs which lead back to the source of any changes made to your AWS environment.
Aws security best practices. 9 AWS Security Best Practices - Alert Logic [ Data Security Best Practices] 6. Backup Your Data You never know if you're going to need to restore data after a breach, so back up your data regularly. You can do this by using AWS Backup. This app makes it easy to automate backups across your AWS environment, so you never have to worry about losing important information. AWS Security Best Practices - AWS Security Best Practices AWS Security Best Practices. AWS Whitepaper. Welcome; AWS Documentation AWS Whitepapers AWS Whitepaper. AWS Security Best Practices. PDF RSS. Notice: This whitepaper has been archived. For the latest technical information on ... PDF AWS Security Best Practices Amazon Web Services AWS Security Best Practices Page 1 Introduction Information security is of paramount importance to Amazon Web Services (AWS) customers. Security is a core functional requirement that protects mission- critical information from accidental or deliberate theft, leakage, integrity compromise, and deletion. AWS Security Best Practices for 2019 | Guardicore AWS security group best practices Now that we've clarified what a security group is, we'll dive into a few AWS security group best practices to help you get started using them. Minimize open ports - Unless there is a highly compelling argument to do so, only allow access to required ports on any given instance.
What is AWS Security? Risks, Best Practices, and More Here are some best practices to help you choose the right solution: Easy integration. Choose a security solution that integrates with AWS to make the process painless. Maintain visibility and control. To be able to effectively audit and control compliance, choose a solution that allows total visibility and control. AWS VPC Security: 13 Best Practices [The 2022 Guide] - Hyperglance The best practice is to split your production, staging, and pre-production environments across different VPCs. Image courtesy of AWS 5. Use Security Groups To Control Resource Access It's vital that you factor in AWS Identity Access Management (IAM) when you're planning and setting up your VPC. Five AWS Security Best Practices | Sumo Logic Five AWS Security Best Practices. Enhancing cloud security through better visibility. Access brief. Thank you for your interest. Download Continuous innovation and speed to market are mandating dynamic paradigm shifts in how companies conceive, develop and implement IT operations and security strategies. The escalating demand for agility is ... 21 AWS Security Groups Best Practices | McAfee Blog Definitive Guide to Securing Workloads on AWS Download to learn about the AWS adoption trends, security challenges and best practices around AWS and applications deployed in AWS. Download Now 6) Outbound access: Restrict outbound access from ports to required entities only, such as specific ports or specific destinations.
AWS Security Best Practices | Classroom Training | AWS Students should have familiarity with AWS services and a strong background in information security concepts, techniques, and paradigms in the areas of networking, operating systems, data encryption, and operational controls. We recommend that attendees of this course have completed: AWS Security Fundamentals AWS Security Essentials Find a class AWS Security Best Practices Checklist | CDW Some practices may be as easy as performing regular data backups or creating appropriate password policies but can go a long way in increasing overall security. By following this checklist, you can help ensure that your cloud-based and in-house services are as secure as possible: 1. Create Strong Password Policies Top 10 security best practices for securing data in Amazon S3 The AWS Foundational Security Best Practices standard is a set of controls that detect when your deployed accounts and resources deviate from security best practices, and provides clear remediation steps. The controls contain best practices from across multiple AWS services, including S3. 7 Cloud Security Issues and AWS Security Best Practices Fixes Top 7 AWS Security Best Practices #1: Insufficient Permissions and Encryptions . Within AWS is the option to store and retrieve data using the Simple Storage Service (S3) infrastructure, also known as S3 buckets. Users can choose to create a bucket within a specific region (anywhere in the world you choose), and upload the data quickly and ...
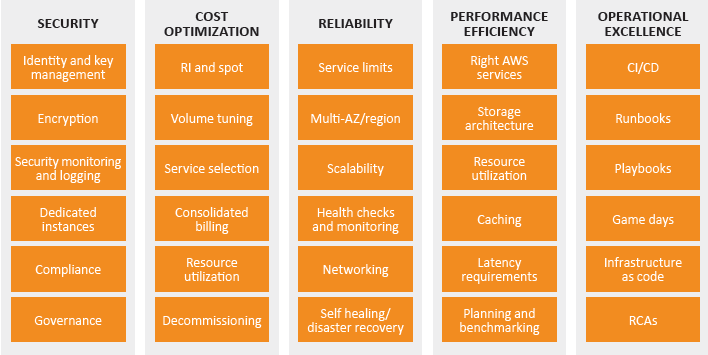
Security - AWS Well-Architected Framework The Security pillar encompasses the ability to protect data, systems, and assets to take advantage of cloud technologies to improve your security. The security pillar provides an overview of design principles, best practices, and questions. You can find prescriptive guidance on implementation in the Security Pillar whitepaper. Topics
AWS Cloud Security: Top Risks, Best Practices, & Tools AWS cloud security best practices are those steps that enhance the available security within the AWS cloud when taken. These solutions include: Data Encryption; Encryption is quite important to keep data that is stored and transmitted in the cloud secure from malicious attacks. It is also a security mandate for some regulatory standards without ...
How To Use AWS Security Hub To Automate Best Practices - Securing The Cloud It automates the checking of security best practices in your AWS environment. It is the central place to look for AWS security alerts and findings as it prioritizes them from many AWS services, such as Amazon GuardDuty, Amazon Inspector, Amazon Macie, AWS Identity and Access Management (IAM) Access Analyzer, and AWS Firewall Manager.
AWS Cloud Security Best Practices: Securing AWS Environments - Rapid7 AWS Cloud Security Best Practices: Securing AWS Environments AWS is as secure as you make it. We break down the security best practices you should follow to secure AWS cloud environments. Learn more. Products Insight Platform Solutions XDR & SIEM INSIGHTIDR Threat Intelligence THREAT COMMAND Vulnerability Management INSIGHTVM
Best Practices | AWS Security Blog The AWS Security team has made it easier for you to find information and guidance on best practices for your cloud architecture. We're pleased to share the Best Practices for Security, Identity, & Compliance webpage of the new AWS Architecture Center.
Security, Identity & Compliance | AWS Architecture Center Best Practices for Security, Identity, & Compliance Learn how to meet your security and compliance goals using AWS infrastructure and services. To learn current AWS recommendations and strategies to use when designing cloud architectures with security in mind, see the Security Pillar - AWS Well-Architected Framework.
Best Practices - Security - Amazon Elastic Container Service Each topic in this guide starts with a brief overview, followed by a list of recommendations and best practices that you can use to secure your Amazon ECS clusters. Topics Shared responsibility model AWS Identity and Access Management Using IAM roles with Amazon ECS tasks Network security Secrets management
51 AWS Security Best Practices | McAfee Blog Below are some best practices around AWS database and data storage security: Ensure that no S3 Buckets are publicly readable/writeable unless required by the business. Turn on Redshift audit logging in order to support auditing and post-incident forensic investigations for a given database. Encrypt data stored in EBS as an added layer of security.




0 Response to "41 aws security best practices"
Post a Comment